Introduction to Small Form-factor Pluggable (SFP) Transceiver Modu...
Introduction to Small Form-factor Pluggable (SFP) Transceiver Modules What Is SFP? SFP, short for small form-factor pluggable i...










































































Visit Fluke Networks for more information about fiber cleaning and inspection: http://www.flukenetworks.com/products/fiber-optic-cleaning-kits There are two types of problems that will cause optical loss as light leaves one end-face and enters another ins
Featured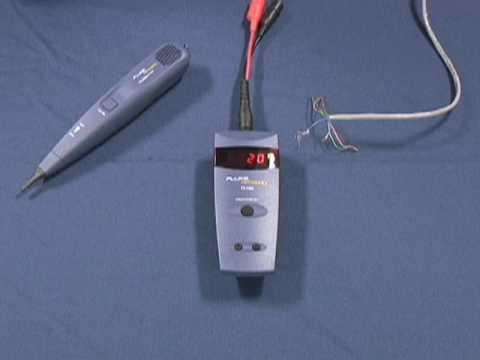
For more information visit www.flukenetworks.com/ts100?ls=yt This is a quick overview of the features and benefits of the TS100 Cable Fault Finder.
Featured
For more information about JackRapid™ Punchdown Tool http://www.flukenetworks.com/datacom-cabling/installation-tools/JackRapid-Punchdown-Tool JackRapid™ is a patented jack termination tool that saves time and increases accuracy by seating and terminating
Featured
What is the difference between single mode and multimode fiber? Neal Allen, engineer and author, tells you why you should care. Learn how light travels through single mode and multimode fibers. Visit Fluke Networks for more information about our fiber tes
Featured
Learn about the importance of fiber testing and what to consider in this 8 part series from Fluke Networks: http://www.flukenetworks.com/Expertise/Learn-About/Fiber-Testing As the need for pre-terminated fiber cabling increases, ensuring optimal network p
Featured
For more information on fiber testing, visit Fluke Networks http://www.flukenetworks.com/Expertise/Learn-About/Fiber-Testing Cable installers should invest the effort to study performance guarantees for pre-terminated fiber trunks to ensure that it protec
Featured
为企业级网络全新设计 Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt
Featured
Für Unternehmensnetzwerke entwickelt Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt
Featured
Construido para las redes enterprise. Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt
Featured
Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt
Featured
企業ネットワーク向けに開発 Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt
Featured
Construído para redes corporativas Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt
Featured
Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt This demonstration outlines how to set launch and tail cord compensation when using the OptiFiber Pro OTDR
Featured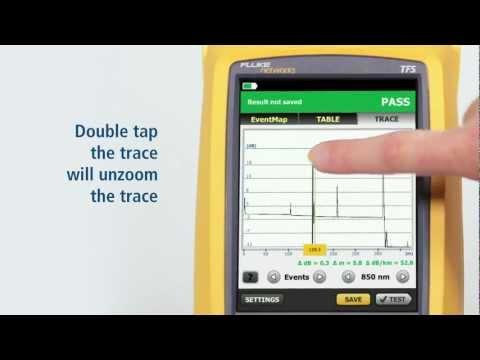
Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt OptiFiber Pro is the first OTDR built from the ground up for enterprise fiber testing. OptiFiber Pro is focused on reducing
Featured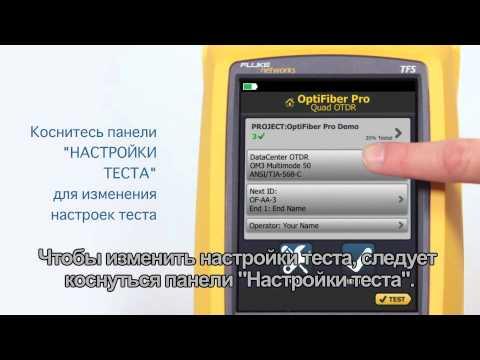
http://www.flukenetworks.com/datacom-cabling?ls=yt Subtitled in Russian, this video shows how OptiFiber Pro OTDR accelerates fiber certification, maximizes efficiency and increases your return on investment.
Featured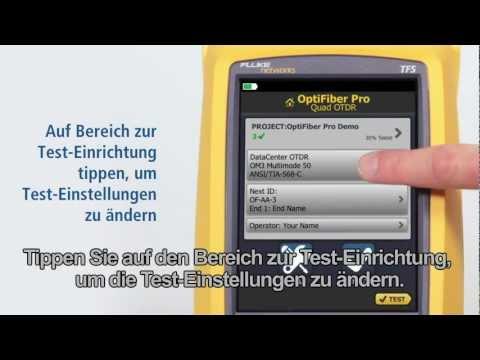
http://www.flukenetworks.com/datacom-cabling?ls=yt Subtitled in German, this video shows how OptiFiber Pro OTDR accelerates fiber certification, maximizes efficiency and increases your return on investment.
Featured
http://www.flukenetworks.com/datacom-cabling?ls=yt Subtitled in Spanish, this video shows how OptiFiber Pro OTDR accelerates fiber certification, maximizes efficiency and increases your return on investment.
Featured
http://www.flukenetworks.com/datacom-cabling?ls=yt Subtitled in Japanese, this video shows how OptiFiber Pro OTDR accelerates fiber certification, maximizes efficiency and increases your return on investment.
Featured
http://www.flukenetworks.com/datacom-cabling?ls=yt Subtitled in Chinese, this video shows how OptiFiber Pro OTDR accelerates fiber certification, maximizes efficiency and increases your return on investment.
Featured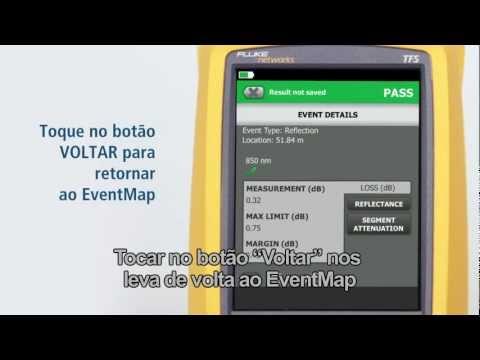
http://www.flukenetworks.com/datacom-cabling?ls=yt Subtitled in Portuguese, this video shows how OptiFiber Pro OTDR accelerates fiber certification, maximizes efficiency and increases your return on investment.
Featured
This demonstration shows how to use FiberInspector and the new OptiFiber Pro OTDR together. For more information on all of our fiber and copper testing tools, please visit Fluke Networks. http://www.flukenetworks.com/datacom-cabling?ls=yt
Featured
Visit Fluke Networks for more info: http://bit.ly/1lc49fy?ls=yt This demonstration outlines how the new user interface works with a trace.
Featured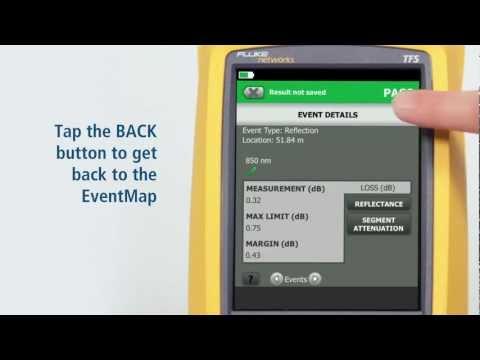
Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt This demonstration outlines how to use the DataCenter OTDR setting on the new OptiFiber Pro OTDR. For more information visit
Featured
Разработан для корпоративных сетей Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt
Featured
Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt This video is a complete demonstration of the new OptiFiber Pro OTDR - the first handheld OTDR built from the ground up for
Featured
Try the OptiFiber Pro OTDR at your site for free! http://www.flukenetworks.com/content/evaluate-optifiber-pro-otdr-your-site?ls=yt See the first OTDR built from the ground up for enterprise fiber testing. OptiFiber Pro is focused on reducing costs while e
Featured
http://www.flukenetworks.com/datacom-cabling?ls=yt Subtitled in French, this video shows how OptiFiber Pro OTDR accelerates fiber certification, maximizes efficiency and increases your return on investment.
Featured